Endoacustica offers, Exclusive Customer Service and free Training
- CATEGORIES
CLOSE
-
Products
- AUDIO SURVEILLANCE
- Spy phones
- Mini voice recorders spy
- Spy earpiece
- Spy listening devices
- * Gsm remote listening devices
- * Analog audio transmitter
- * Encrypted audio transmitter
- * Landline bugging devices
- Analog Digital Transceivers
- Listen through walls devices
- Shotgun Microphone
- Voice Changers
- Mobile phone interception
- VIDEO SURVEILLANCE
- TRACKING DEVICES
- COUNTERSURVEILLANCE
- GADGET
- AUDIO SURVEILLANCE
- Solutions
- Company
- Services
- Contacts
- Blog
Encrypted mobile phone for secure calls
- Double military-grade encryption algorithmm
- AES256 encrypted calls and messages
- Anti-IMSI-Catcher security system
- Impenetrable and anti-chip-off hardware
- OS without backdoors
prod cod: CP-700

Free customer service:
📞 Pre-Sale assistance
🧑💼 Dedicated consultation service
🛠️ After-Sales 🎓 Training and Support
🆘 Technical and operational support
The CP-700 is an encrypted mobile phone designed specifically for professional users. It offers 360° protection, including a secure operating system, baseband firewall, tamper-resistant hardware, and end-to-end encryption for calls and messages.
Secure Calls
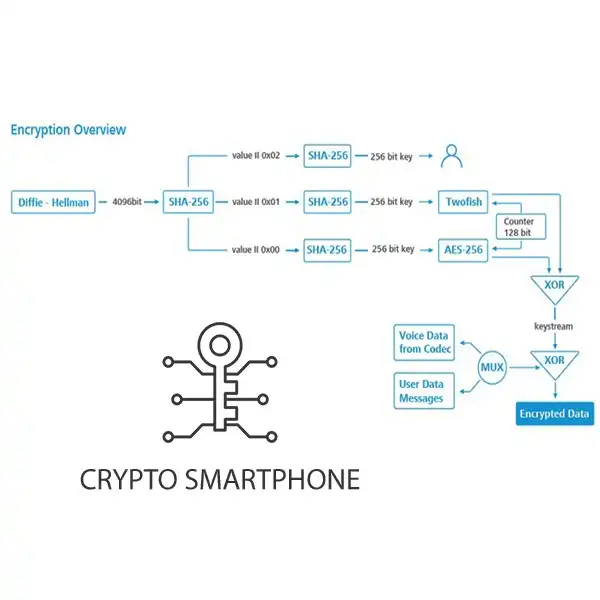
The CP-700 offers secure voice calls with end-to-end encryption over any 2G, 3G, 4G, 5G, or WLAN network, using the strongest available algorithms such as AES256, Twofish, and Diffie-Hellman key exchange with 4096-bit and SHA-256 hash function. The Authentication Key is based on the readout-hash method and the encryption keys are generated autonomously and erased securely and immediately after each call.
Secure messaging
Secure messaging is highly secure due to its use of robust encryption algorithms. It employs the Diffie-Hellman cryptographic protocol with 4096-bit encryption, as well as message encryption using AES256 and Twofish with 256-bit keys.
Specifically, the encrypted cellphone utilizes the two best cryptographic algorithms available, ensuring the highest levels of protection for encoding operations. This combination of the strongest encryption system and a 256-bit key length provides maximum security.
Protected operating system with secure boot
The Android Secure operating system is a ground-up creation optimized for communication security, boasting security-optimized communication components and providing precise customization and control over OS security levels.
The secure boot chain system uses cryptographic keys to verify the bootloader, kernel, recovery mode, kernel objects, and APK applications during boot. This ensures that every component of the operating system has been digitally signed and is trustworthy.
The system and device software undergo continuous real-time integrity checks to detect any unauthorized modifications. The device can respond appropriately by sending an alert or blocking until the issue is resolved.
Configurable OS security settings
The hardware module controller and permission enforcement module work together to enable you to control access to your network, data, and various sensors such as cameras and microphones. This helps you maintain individual security policies that suit your needs.
Firewall Baseband 2.0
Firewall Baseband 2.0 is an advanced security feature capable of detecting and countering attacks through the airwaves, by activating the necessary security measures. Moreover, it is capable of automatically detecting and blocking IMSI Catcher devices and rogue base stations, which can simulate legitimate cell towers to intercept device communications.
Firewall Baseband 2.0 can identify attempts to track a user's location through silent SS7 or SMS messages and activate the necessary countermeasures to protect user privacy.
Secure Anti-Tampering Hardware
The hardware design of the encrypted CP-700 phone is designed to be tamper-resistant, thanks to the use of dedicated hardware security modules. These include screen removal detection circuits and environmental fault protection (EFP), capable of monitoring temperature, voltage, clock frequency, and more, supporting FIPS 140-2 and Common Criteria security requirements.
The CP-700 encrypted phone is impenetrable to attempts at forced data extraction or chip-off, as the flash memory is integrated irreversibly.
The CP-700 smartphone was created to offer high security thanks to its ad hoc design and construction. Unlike common smartphones, which may be vulnerable to cyber-attacks using known and accessible hardware components, CP-700 smartphone uses hardware components that are not easily accessible, making it difficult for unauthorized individuals to access and compromise the device's security.
The CP-700 encrypted phone ensures maximum security with its TPM chip
The TPM chip in the CP-700 is compliant with Trusted Computing Group (TCG) level 2 version 1.2, revision 116 specifications. Its ability to measure and attest to the platform ensures that the phone has booted securely and has not been tampered with by third parties.
The CP-700 also features an active shield and environmental sensors that constantly monitor the surrounding environment to ensure that the phone has not been compromised. Additionally, the presence of a Memory Protection Unit (MPU) ensures that the device's memory is protected from potential attacks.
The CP-700 is designed to prevent tampering by third parties through hardware and software protection against fault injection, a common attack method where an attacker intentionally introduces a fault into the system to gain unauthorized access to the device's data or functionality.
Encrypted Data Storage
CP-700 uses an encrypted storage system in order to secure contacts, messages, and notes. It has smart folders that protect data at rest from unauthorized access.
Encrypted storage is a data storage technique in which data is encrypted to allow only authorized personnel to decrypt and access it. This means that even if an unauthorized person gains access to the encrypted data, they cannot read the content without the decryption key.
Verifiable source code
The CP-700 is one of the few secure encrypted phones on the market with verifiable source code available for independent security evaluations, allowing for code inspections in compliance with national and international verification and certification standards.
This ensures the integrity of the device, proper implementation of encryption algorithms, and absence of any backdoors.
NOTE: CP-700's protection is activated on the communication between two phones, so at least a pair of devices is required for it to work.
*Images are subject to change without notice.
Dimensions: 158,6 mm * 74,8 mm * 8,9 mm
Weight: 207 g
Water Protection: IP67
Display: 6.4" (1080*2400) Color AMOLED, 410 ppi
Camera: 50 MP with phase-detection autofocus and LED flash
12 MP for front facing applications, 3840*2160 video capture and playback, both cameras can be disabled
Audio: High-performance speakers, multi-microphone ANC
CPU: S5P9845 (GS101) 64-bit octa-core CPU, 3072 Kbyte L2, 4096 Kbyte L3, ARM Mali-G78MP20 GPU
Graphics accelerator: QDSP
External memory: Micro SD-CARD
Connectivity: - GSM/GPRS/EDGE (850/900/1800/1900MHz)
- UMTS/HSDPA+ (B1, B2, B4, B5, B6, B8),
- LTE Advanced(3GPP, FDD, IMS, VoLTE, Carrier Aggregation, B2, B3,B4 , B5, B7, B8, B12, B13, B14, B17, B18, B19, B20,B25, B26, B28, B29, B30, B32)
- 5G NR (N1, N2, N3, N5, N7, N8, N12, N14, N20, N25, N28, N30, N66, N71)
- USB Type C connector with USB 3.2 Gen 2 (fast charging),
- USB Power Delivery 2.0/3.0, Wi-Fi 802.11 a/b/g/n/ac/ax
Secure communication between two or more mobile phone users, including calls, messaging, and data exchange, ensuring complete safety and privacy.
Our solutions ensure that your phone conversations, messages, and data exchanges are secure and private, and we take every precaution to prevent unauthorized access to your device.