Endoacustica offers, Exclusive Customer Service and free Training

Encrypted phone 🔰📱
What is an encrypted phone?
An encrypted phone, also known as a security phone, provides military-grade encryption. These devices are highly reliable and cannot be cracked or decoded. This secure phone is perfect for those who want to protect their privacy and keep data safe and secure.
Endoacustica offers the most secure phone on the market. Our wide range of the most secure phones includes: Encrypted Android Phones, Secure Landline Phone, Stealth Phones, Encrypted Communications Radios in S-Band, and Encrypted Satellite Phones. All of these devices provide military-grade security.
What is an encrypted phone?
An encrypted phone, also known as a security phone, provides military-grade encryption. These devices are highly reliable and cannot be cracked or decoded. This secure phone is perfect for those who want to protect their privacy and keep data safe and secure....
Endoacustica offers the most secure phone on the market. Our wide range of the most secure phones includes: Encrypted Android Phones, Secure Landline Phone, Stealth Phones, Encrypted Communications Radios in S-Band, and Encrypted Satellite Phones. All of these devices provide military-grade security.
Read More

Intrusion detection system for Android and iPhone
ENDO-MDP is an advanced Mobile Device Protection (MDP) solution designed to protect mobile devices from sophisticated cyber threats. Built on artificial intelligence and behavioral analysis,...

ENDO-STEALTH - The Smartphone for Total Security
Endo-Stealth is the ultimate smartphone for those seeking maximum security, anonymity, and advanced protection against surveillance and interception. Built on a high-end Samsung device ...

Encrypted voice and messages GSM mobile phone
There is no protection against IMSI-catcher based eavesdropping devices, except using end-to-end call encryption. The CP-700 smartphone is a secure communication mobile phone based...

SecureCall - The Encrypted Secure Smartphone with 5G connection
The SecureCall secure smartphone, provides a wide protection against privacy threats. This secure smartphone integrates different levels of security.

Encrypted smartphone with anonymouse SIM card
The secure CRYPTO STEALTH smartphone is the best mobile phone in the world in terms of privacy and communication safety, as it makes use of active and passive defense systems...
Untraceable Stealth Phone mobile
The Stealth Phone allows you to achieve a high level of protection against the risks of interceptions, now more and more common when you use an unprotected mobile phone...

New Untraceable dual SIM Stealth Phone Plus
Stealth Phone Plus protects the user against mobile eavesdropping. Besides the Stealth Phone's basic protection it provides: GSM isolation function, advanced cryptographic...

IP PTT Mesh Radio for critical scenario
Handheld PTT Mesh Radio: Secure and encrypted communications device in the S-Band. Equipped with the 'Seek & Avoid' feature to bypass Jammered frequencies, ideal for challenging critical environments.

Anti-interception VOIP landline phone
The anti-wiretapping VOIP landline phone is a suitable device for confidential conversations. Don't fear of being overheard, the system is supplied with...

New encrypted VOIP landline telephone
The VOIP encrypted SECURE IP PLUS telephone allows you to have secret conversations via landline phone. Avoid any wiretapping operations with our secure phone...

Encrypted satellite cell phone
This encrypted satellite phone uses GSMK Cryptophone System to enables you to put the trust where it belongs in a trustworthy, open and...

Chatmail PGP encryption software
ChatMail PGP uses encrypted email messaging and other security tools to protect users at any time against hackers or malicious people. The app can be...
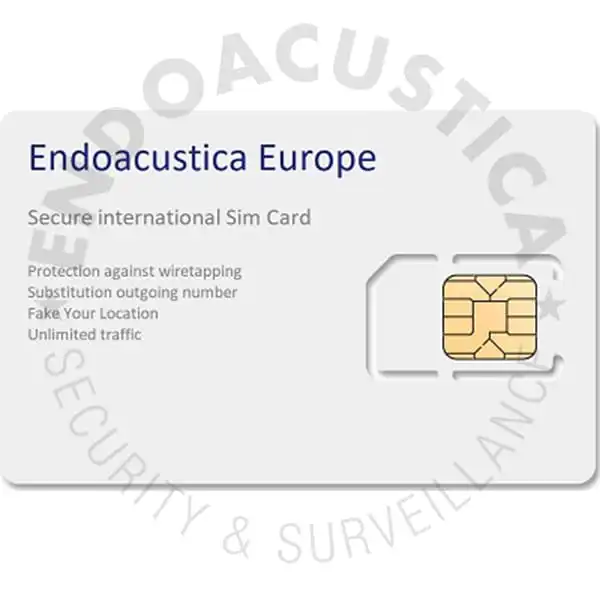
Aanonymous SIM card
Secure SIM Card is an anonymous SIM card. All communications from and to the secure sim are nor managed through a private undetectable network and not through international providers...
FAQ
There are several types of encrypted mobile phones, each of them has different functionalities coming from highly sophisticated technologies and software that allow users to make phone calls without being listened to and then talk securely. Additionally, encrypted smartphones are very requested to manage cryptocurrency Bitcoin and Altcoin accounts securely; for digital currencies in general. In the range of anti-tapping phones, there are two main types of devices: encrypted mobile phones and stealth phones. Let’s see together their main features.
Encrypted mobile phones
Encrypted mobile phones allow users to make confidential phone calls with military-grade encryption like AES256 or Two Fish 256, only if they are paired with another encrypted mobile phone. It means that these encrypted mobile phones provide the best performance when used paired with another device with the same operating algorithm.
Stealth Phone
Stealth phones, instead, work on the mobile phone ID number, known as IMEI (International Mobile Equipment Identity), by changing it any time users decide to. It’s a numeric code that identifies the mobile device uniquely, being it a mobile phone or a GSM modem.
Stealth Phone Plus
A Stealth phone plus has some additional features such as the dual SIM, which are: protection against active tapping devices, geo-localization camouflage, and an advanced encrypting system for text messages.
Explore our portfolio, check features and costs of our encrypted devices and choose the most suitable for your needs. Your privacy is important, let’s protect it from external risks. Don’t leave your conversation at the mercy of everybody! Endoacustica Europe helps you to identify the most suitable encrypted mobile phone for your needs!
A security phone is a device designed with enhanced security features to protect your sensitive data and privacy. These phones typically offer advanced encryption, secure boot processes, and robust authentication mechanisms to safeguard against unauthorized access and data breaches. Considering a security phone is essential for individuals or organizations handling confidential information or concerned about privacy in an increasingly digital world.
The most secure phones prioritize features such as end-to-end encryption for calls, messages, and data transmission, robust biometric authentication (e.g., fingerprint or facial recognition), secure hardware components (e.g., tamper-resistant chips), frequent security updates, and a strong app permission model. Additionally, reputable security certifications and a commitment to privacy-focused practices are indicators of a truly secure device.
Yes, there are several encrypted Android phones available from various manufacturers. These devices come preloaded with security-focused features such as built-in encryption for data storage, secure boot processes, and encrypted communication channels. Users can also enhance security by leveraging additional encryption tools and features available on the Android platform.
Encryption smartphones protect your data by scrambling it into unreadable ciphertext using complex algorithms. Only authorized users with the decryption key can access the original information. This means that even if your device is lost, stolen, or hacked, the encrypted data remains inaccessible to unauthorized individuals, providing a strong layer of protection for your sensitive information.
Fully encrypted phones are available for sale from reputable manufacturers and authorized retailers specializing in privacy-focused technology. These devices are often marketed explicitly for their security features, and they may come with additional privacy-centric services and support. It's essential to research and choose a trusted vendor to ensure the authenticity and effectiveness of the encryption features.
