Endoacustica offers, Exclusive Customer Service and free Training
- CATEGORIES
CLOSE
-
Products
- AUDIO SURVEILLANCE
- Spy phones
- Mini voice recorders spy
- Spy earpiece
- Spy listening devices
- * Gsm remote listening devices
- * Analog audio transmitter
- * Encrypted audio transmitter
- * Landline bugging devices
- Analog Digital Transceivers
- Listen through walls devices
- Shotgun Microphone
- Voice Changers
- Mobile phone interception
- VIDEO SURVEILLANCE
- TRACKING DEVICES
- COUNTERSURVEILLANCE
- GADGET
- AUDIO SURVEILLANCE
- Solutions
- Company
- Services
- Contacts
- Blog
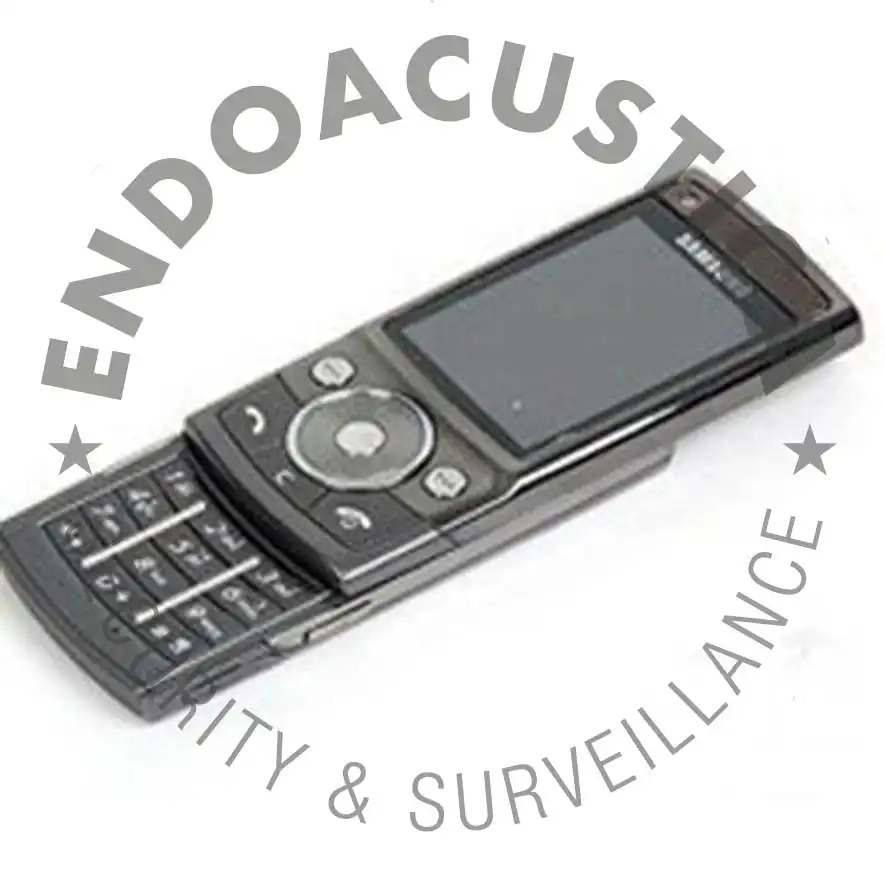
Untraceable phone with anti interception function
- Warning of any interception attempt
- Dinamic IMEI changing
- A5 level setting
- Anti Ping function
- GSM Interceptor Proximity Alert
prod cod: STEALTH-PHONE

Free customer service:
📞 Pre-Sale assistance
🧑💼 Dedicated consultation service
🛠️ After-Sales 🎓 Training and Support
🆘 Technical and operational support
"Ghost" cellphone that cannot be intercepted. It reports any interception attempt!
For the security of your phone conversations, the Stealth Phone allows you to achieve a high level of protection against the risks of interceptions, now more and more common when you use an unprotected mobile phone. Unlike a cell phone that operates on the encrypted data item, codifying and making them unintelligible to any outside listener, the Stealth Phone protects the call itself, making the phone untraceable and impossible to localize.
This result is obtained thanks to the IMEI dinamic chamging (identification code transmitted to your telephone provider), but above all to an elaborate analysis algorithm of the telephone network to which you are connected. The wiretaps can be based on the IMEI number or on the phone number. So in case the interception is performed starting from the knowledge of your IMEI number, changing the SIM card will not help, because it's the device itself to be intercepted.
Ultimately, by having the ability to change the IMEI you get the same result as an effective and real change of cellphone. And that's not all. The Endoacustica Stealth Phone will alert you immediately by a vibrating display text message when someone will try to intercept you.
The active equipment, normally used in wiretapping as the IMEI/IMSI catcher and GSM Interceptors, works on the A5 security level, masking itself as a new cell tower to connect to. Once hooked, the phone can be intercepted on voice and data.
This excellent device has the same features as a Burner phone or a trap phone, but you don't need to trough it out after use.
In addition, the Stealth Phone is equipped with the Fake Cell Tower Blocker function(the fake cell tower duplicated by a GSM interceptor). This intelligent function, allows users to block the phone on a specific GSM channel number (called ARFCN) within your area.
The Stealth Phone main features
1. Dinamic IMEI changing.
2. A5 tracking feature:This function is intended to protect the telephone against wiretapping carried out with GSM active and semi-active.
3. UnPing feature: When the GSM interceptor is trying to locate your mobile phone, users will receive location tracking pings alert.
4. Channel lock: This feature will allow users to lock the phone to a specific GSM channel number (called ARFCN) within your area.
5. Shows of TMSI: This is the temporary identification that the GSM network assigns to the mobile phone, and will change when or if the phone is switched off / on. It will also change if the phone loses full network reception.
6. Automatic clearing of the call log.
7. Call recording.
8. Safe against forensic analysis: The phone is not accessible, cannot be examined by forensic software and hardware. Firmware cannot be read / written or cloned. The phone is not accessible, readable or scannable by any mobile forensic equipment. Physical checkout and file system checkout are blocked by a security filter. Phones cannot be accessed via forensic software and hardware. Firmware cannot be read / written or cloned.
Brand new Stealth Phone Plus version
The undetectable STEALTH-PHONE mobile is also available in the new PLUS version equipped with double SIM card, geographic position masking, GSM isolation, SMS encryption, calls via server and much more.
ATTENTION!
The company is not responsible in any way for the change of IMEI number. The phone comes with original IMEI and any changes are under the customer's control. Furthermore, the device is made available only for the warning function in the event of interceptions by third parties. The company disclaims any liability for any misuse.
Cell phone: Stealth Phone ( Samsung G608 )
Network GSM: 850 / 900 / 1800 / 1900
SIM: Mini-SIM
Dimensions: 101 x 47.8 x 14.9 mm (3.98 x 1.88 x 0.59 in)
Weight: 104 g (3.67 oz)
Display: microSD
Memory Card slot: 3GB
Data: GPRS Class 10 (4+1/3+2 slots), 32 - 48 kbps
EDGE: v2.0
Front camera: 5 megapixel
Bluetooth: v2.0 with A2DP
USB: v2.0
Camera: 5 MP, autofocus, LED flash
GPS: NO
Battery: Li-Ion 880 mAh (300h stand-by / 3,5h chiamata)
For protection of mobile phone conversations of important people, managers etc.
For secure mobile phone communication in the field of investigations
For protection of one's privacy both in the workplace and in the private sphere